Architecture
Blackwall operates as an intelligent traffic control layer sitting in front of your infrastructure, making real-time access decisions and ensuring that only legitimate, high-quality traffic reaches your applications.
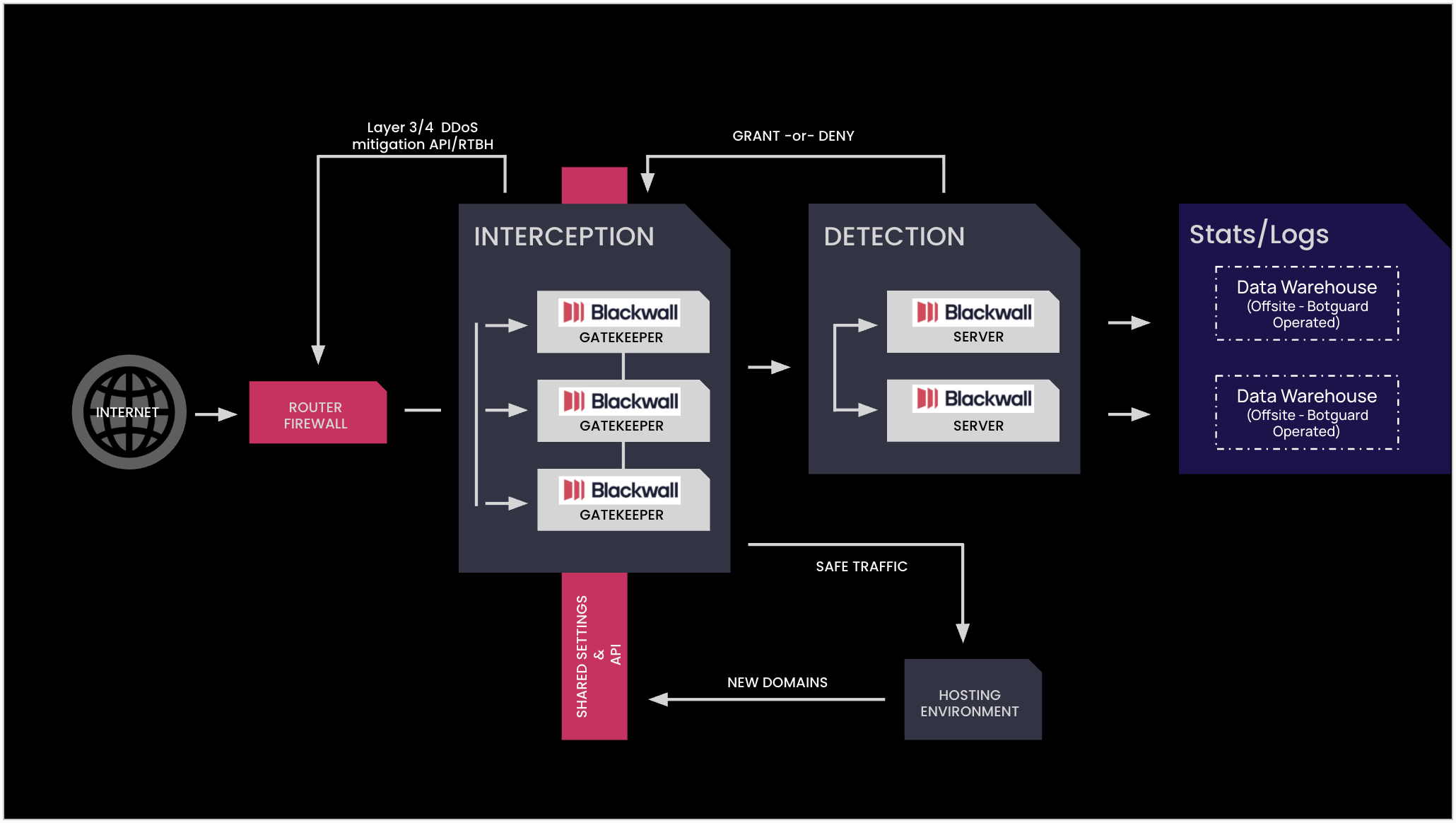
The following diagram illustrates a typical Blackwall deployment model, where inbound internet traffic is filtered, analysed, and controlled before it ever reaches the protected hosting environment. At the edge, traffic first passes through standard network controls (router/firewall and optional L3/4 DDoS mitigation), before entering the Interception layer, where a single or multiple GateKeeper nodes act as a reverse proxy. GateKeeper is the first line of defence, hiding the origin infrastructure and filtering requests in real-time, blocking malicious bots, rate-limiting suspicious clients, and mitigating application-layer (L7) DDoS attacks, while allowing legitimate users through.
Once traffic is accepted, it moves to the Detection layer, where dedicated Blackwall servers perform deeper behavioural analysis and decisioning (grant or deny). This layer uses techniques such as session analysis and bot detection to distinguish real users from automated or malicious activity, even in complex scenarios. “Safe” traffic is then forwarded to the hosting environment, while logs and telemetry may be exported to offsite data warehouses (optional) for monitoring, analytics, and rule tuning. This architecture not only improves security by filtering threats early, but also enhances performance and scalability by distributing load and reducing unnecessary traffic reaching backend systems.