FAQs
General and compatibility questions
I have an e-commerce website, but I am not sure if I need Blackwall's services. How can I check if I need Blackwall's protection?
In recent years, bad bot traffic has grown so much that virtually any eCommerce website can benefit from using some kind of traffic management tool. You can easily perform a rapid scan of your website to check its current protection. This very simple scanner emulates access to your website with fake search engines, popular commercial bots, and browser emulators. This rapid test takes less than one minute and it will provide all the information that you need to make an informed choice about what Blackwall can do for your online business.
What if you block some necessary bots by mistake?
BotGuard have developed a special method to avoid false positives. Blackwall lets you start monitoring your automated traffic in no blocking mode. The website administrator is then advised by our AI Advisor to enable blocking rules one by one, based on your traffic. The Blackwall dashboard enables you maintain and fine tune custom blocking rules. If any identified threat requires your attention, you are notified by email.
Does Blackwall impact on search engines website indexing?
No, search engines like Google, Bing, Yandex and others continue to access your website as usual.
Do you protect websites against DDoS attacks?
No, Blackwall doesn't provide a service against Distributed Denial-of-Service (DDoS) attacks. Typically, such an attack is targeted against the network infrastructure in an attempt to overload its resources. However, if protection against volumetric-DDoS attacks is provided, Blackwall is a great addition, since it can resist Denial-of-Service attacks at the application level (L7), blocking the bots' access to the web application.
I already use anti-DDoS protection. Do I still need Blackwall's protection?
Yes, this is our basic recommendation. It's important to note that Blackwall does not provide anti-DDoS protection. Rather, we integrate at the web server level to manage bot traffic (e.g. scrapers, content theft, competitive monitoring, hacker attacks). The most sensible approach is to combine the two forms of protection. For example, some of our partners combine Cloudflare for DDoS protection with our service for bot management, since our system is based on digital fingerprinting and can be fine-tuned to the needs of a particular website.
I use a Web Application Firewall (WAF) with custom rules. Can I still use Blackwall services for bot protection?
Yes, you should combine your existing WAF with Blackwall's bot management service. You do not have to use our WAF at all. We already have a number of users who take this approach.
Do you provide web application vulnerabilities scanning?
No, the Blackwall service analyzes your traffic, identifies the visitor, and helps your server correctly process the request in accordance with your own settings. We do not monitor your website security.
What about human visitor's privacy? Where do you store the traffic data?
The short answer is we don't. We process the content of a website visitor's request, but we do not store this data. We process it dynamically and we do not use digital identifiers such as cookies or fingerprints that attribute requests to the unique user.
Do you have a demo?
Yes, we have a demo website at demo.botguard.net, which is protected with the Blackwall Cloud Website Protection service. You are welcome to try emulating any bot or human traffic to our demo site and check whether the bots are blocked by Blackwall's service.
Which languages does the Blackwall dashboard provide?
We currently provide an interface in English. The appropriate localized version is set up automatically according to the OS/browser language. We have a number of localized versions currently under development.
Do you use captcha?
Blackwall does not use captcha by default. Normally, neither user action like captcha or additional input is required. However, you can configure the blocking policy so that captcha is used in doubtful cases. For most of your website users, nothing will change with their service.
Does using Blackwall increase website response time?
Yes, the website response time can increase slightly due to the website visitor filtering. Fortunately, it's not more than a few milliseconds. Blackwall servers are located close by to ensure high speed and minimal network latency.
I can't login to my site control panel. I am blocked.
Blackwall blocks access to the website admin pages for security reasons. You can create a special custom rule based on your IP address (Blackwall supports both IPv4 and IPv6), or allow access to these pages from any address. To add a special custom rule, open the Rules Editor page and create a new rule based on your IP address (Blackwall supports both IPv4 and IPv6). Refer to Custom Rules for more information.
To allow access to everyone, create a rule (or a set of rules) allowing access to specific pages. For example, if the admin pages URL starts with http://example.com/admin/, then you can add a regex ^\/admin\/ to the rule to allow access to all of these pages.
Do you use blacklists? How often do you update your threat sources?
We use various databases as sources of "blacklists". This includes IP addresses (BotGuard supports both IPv4 and IPv6), autonomous system numbers, geolocation and software fingerprints. Data related to global attacks, such as DDoS, is updated online. Other databases are updated less frequently, usually every few days. You do not need to take any action to update, this is done automatically in our cloud.
Does Blackwall support HTTP/2 fingerprinting?
Yes, HTTP/2 fingerprinting is simply another passive signal that Blackwall uses to help distinguish legitimate clients from bots. In practice, Blackwall analyzes subtle aspects of the HTTP/2 handshake (frame ordering, settings, priority behavior, etc.) alongside its existing signals to improve detection accuracy. This capability is enabled by default without any user configuration or UI changes. If you are running Blackwall’s Apache integration, the fingerprinting module installs alongside our SSL fingerprinting module and quietly gathers data whenever HTTP/2 is in use. If HTTP/2 is not enabled, it simply does nothing. There are no new settings to tweak, no visible impact on logs (outside of trace‑level debugging), and no actions required. Clients will not experience any noticeable difference, but this section helps to explain why we have it.
How do I get Beta / Early-Access to GateKeeper?
What is 'Early Access'?
Blackwall publishes Gatekeeper builds through two channels:
-
Production repository (recommended): This is the stable, fully tested release repository intended for the majority of customers. This is the default path in all GateKeeper Version Installations and it is what the versioned documentation is written against.
-
Test Repository (Beta / Early-Adopter Channel): This is a faster-moving repository that may contain new features and urgent minor fixes. For example, time-sensitive patches added by the Blackwall team for specific customer environments before they reach the production repository.
You should only use the test repo when you are in one of the following categories:
- An early adopter/beta tester.
- The Blackwall team explictly asks you to.
- When you need an urgent fix that's not yet available in the production repository.
Caveats Before Using the Test Repository
Before using the test repository, it's important to consider some important points:
- Since the test repository tracks newer builds, it may be less stable than production and it may contain regressions or incomplete validation compared to production.
- In future, it may also have different assumptions or minimum requirements than the latest stable release documented in the versioned guides. If using the test repository, make sure to follow this specific guide in this expandable section.
- If you follow version-specific documentation (e.g., v1.4.x or v1.5.x) while installing “latest” from the test repo, you may end up with a build/documentation mismatch, which can cause confusing setup behavior and false bug reports.
- Issues/bugs encountered on the test repository may not reproduce on production. If you encounter a problem while using the test repository, the first troubleshooting step is to switch back to production and confirm whether the issue still occurs. Remember to treat the test repository as a beta version. Always share details if something breaks, such as versions, logs, environment information, and keep a rollback plan so that you can return to the production repository quickly.
How do I Access the Test Repository?
As a prerequisite to installing Blackwall's GateKeeper, you must have Debian installed cleanly on your sytem at a minmum of version 12. Then you must add a Blackwall GateKeeper Debian repository and install packages, as described in the following steps:
-
Import the Blackwall package digital signature key by executing the following two commands:
-
Add the Blackwall test repository to your system repositories by executing the following two commands:
-
Install the latest version of Blackwall's GateKeeper by executing the following two commands in sequence:
-
Reboot your server to apply the changes to your operating system.
As an Early Adopter, How do I Report Bugs or Request Features?
If you choose to use the test repo, you should treat it as a beta path and tell us what you find. Feedback from early adopters is one of the fastest ways that we can catch real-world issues before they reach the stable release repository. When you find a bug or unexpected behavior, please report it as soon as possible to our Support team and include enough detail for us to act quickly. You should include:
- your Gatekeeper version/build.
- OS/distribution.
- install method.
- relevant configuration.
- any logs or error output.
Clear reports help us to reproduce issues, confirm whether they’re specific to the test build or the environment, and ship fixes faster for everyone.
We also welcome feature requests from test-repo users. If there’s a capability you’d like to see, or an improvement that would make Gatekeeper easier to operate in your setup, raise it alongside your feedback. Early input helps us validate product direction, prioritize the right work, and refine features while they’re still evolving.
To report issues and request features, please refer to our Support page in the documentation.
Can I receive a monthly activity report for domains in my account?
Yes, you can. Refer to instruction in the Accounts/Subscriptions page to subscribe to monthly reports. Following subscription, on the last day of each month you will receive separate emails for each domain being protected in your account. If you have 12 domains, you will receive 12 emails. Each email will contain a PDF report for the associated domain. These emails are sent to the email address associated with the account used to subscribe to the reports, but MSPs/Distributors can configure email forwarding rules for these emails if needed, to enable subaccount owners to receive the reports.
Technical issues
I have a WordPress website on an Apache web server. Which integration method is recommended?
We recommend integration at the web server level, as in this case the recognition quality is higher. In the event that this is not possible, you can integrate at the Content Management System (CMS) level with our WordPress plug-in.
Can I use API connectors to integrate with Blackwall?
Yes, we provide an API for our partners to manage websites on their account. Typically we use this API in hosting panel integration modules. The documentation is available at SwaggerHub.
I have several websites in my account. Is it possible to see bot activity by website?
Yes, you can easily use the filter located above the log grid to filter the results that you want to see.
I would like to be able to click on Blocked Bots to see more detail.
You can do this by clicking on the link Add/Edit the rule.
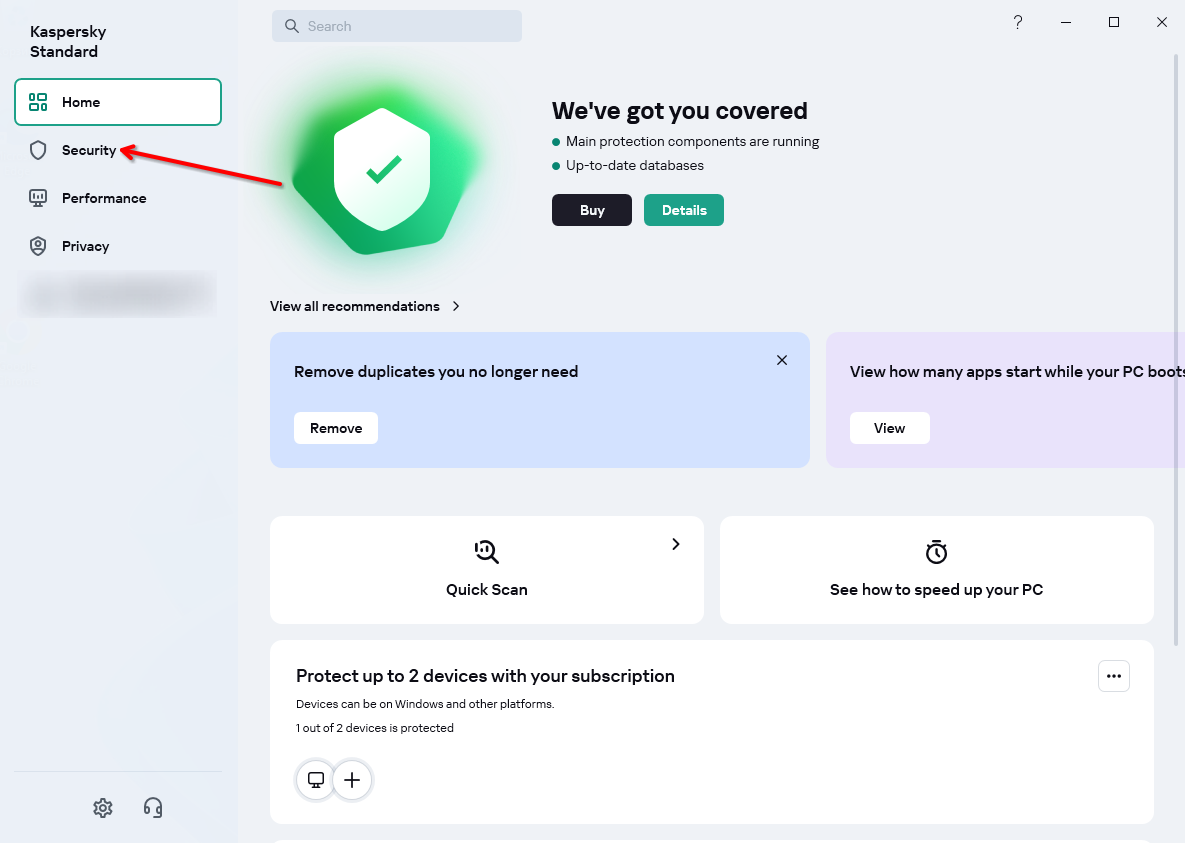
I have Kaspersky or ESET NOD32 antivirus software and cannot access a protected site.
Antivirus MITM Proxy Help -You might experience issues getting to a protected website if you’re using Kaspersky or ESET NOD32 antivirus software. In this case, your visit in Event log will be recognized under Suspicious Behaviour category, with Probable MITM detected in Trigger details.
It might happen due to usage of built-in MITM (Man-In-The-Middle) proxy, which is used to decrypt HTTPS websites traffic. Such practice is questionable because on contrary in some scenarios and implementations it actually might lower your web traffic security, but it’s the only way for antivirus software to take a look into your encrypted web traffic.
Note
Please consider enabling CAPTCHA mitigation for Suspicious Behaviour category. This way, the users that are able to solve CAPTCHA challenge would be granted with access to your website
MITM proxies implemented by Kaspersky and ESET are known to modify your web browser digital fingerprints. And your web request might look to be made by non-original software, and it would be detected as bot by our request analysis engine.
There might be various workarounds for the issue.
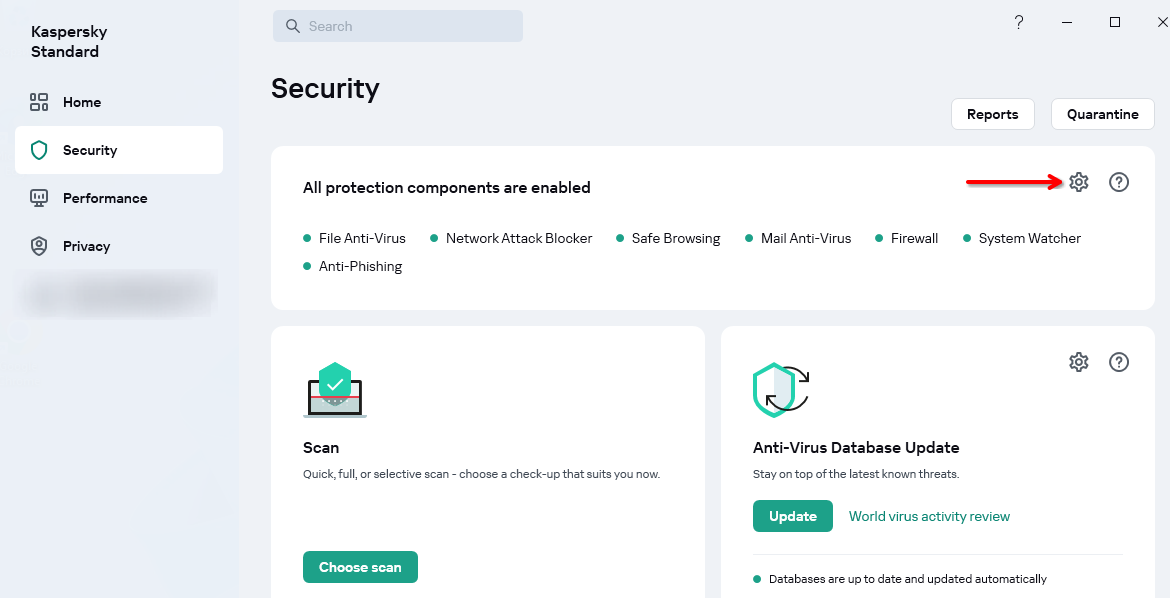
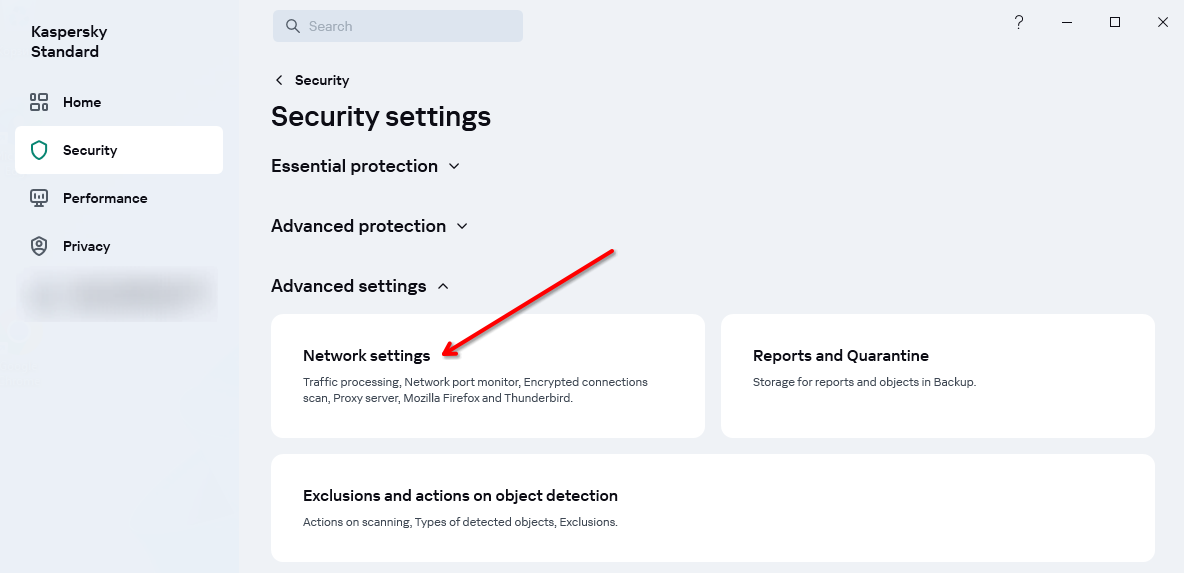
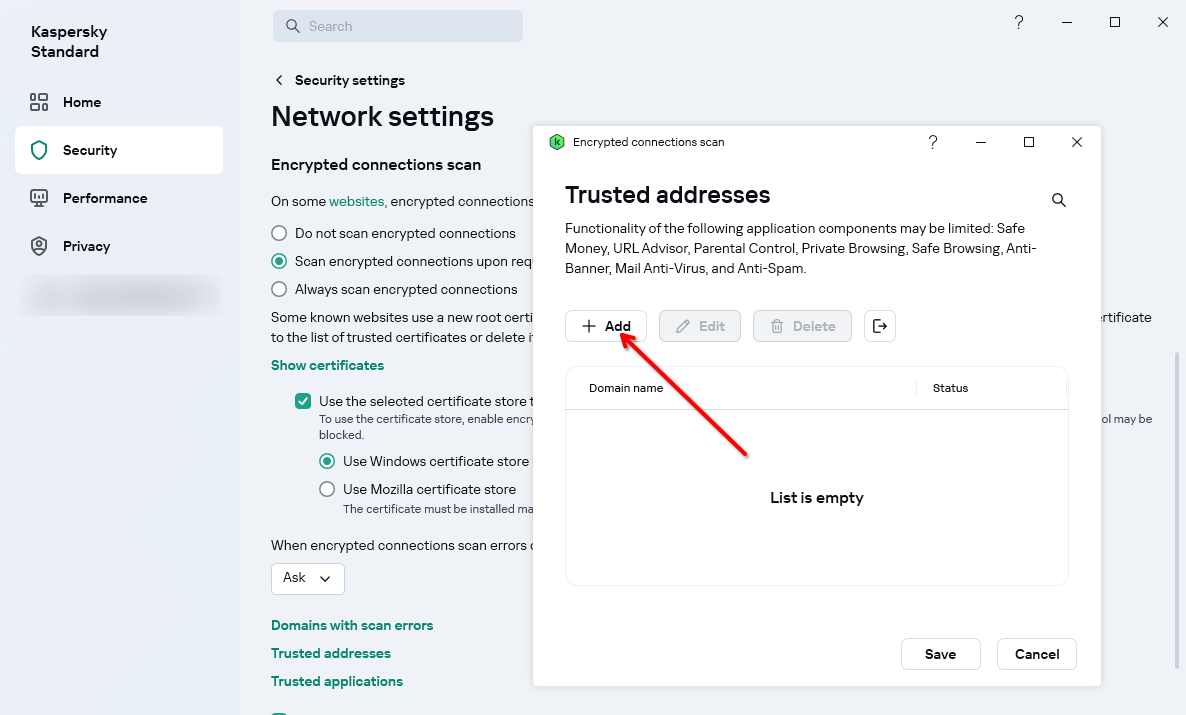
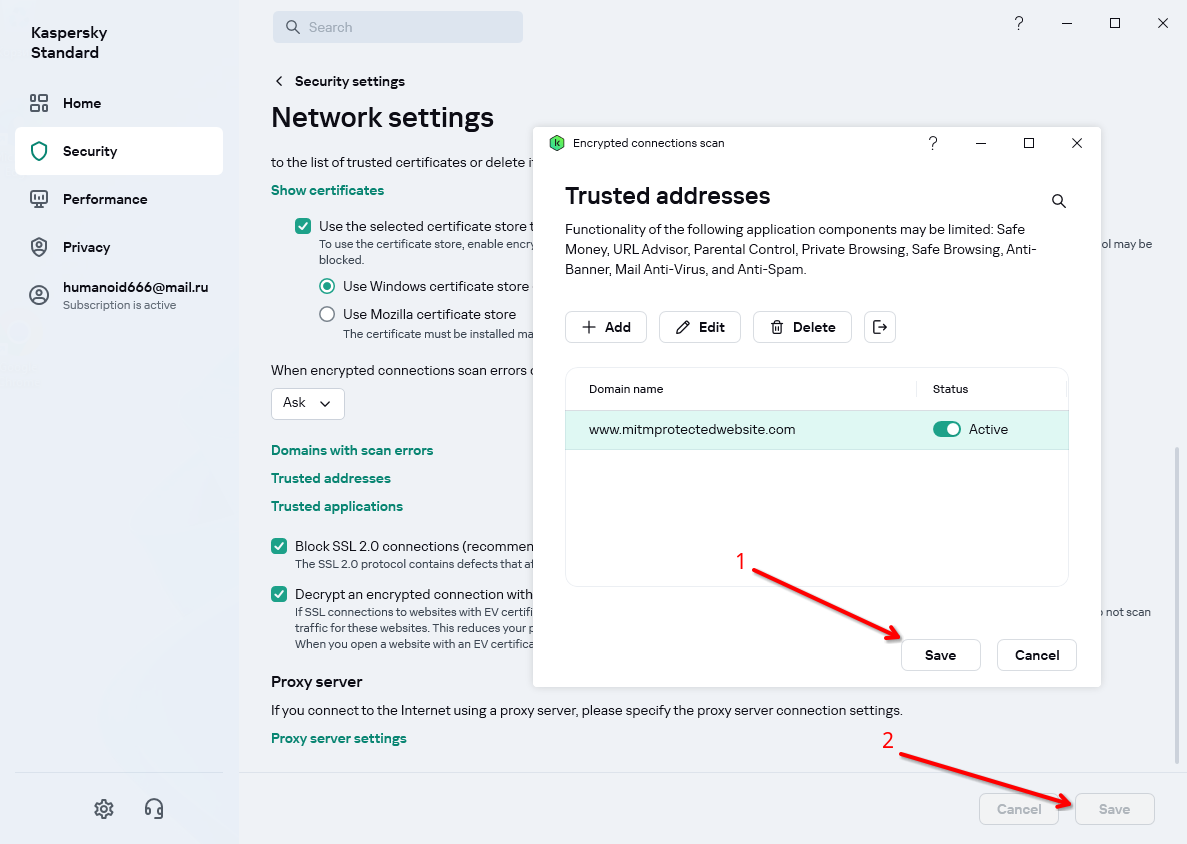
Kaspersky
Whitelist your protected website for Kaspersky
-
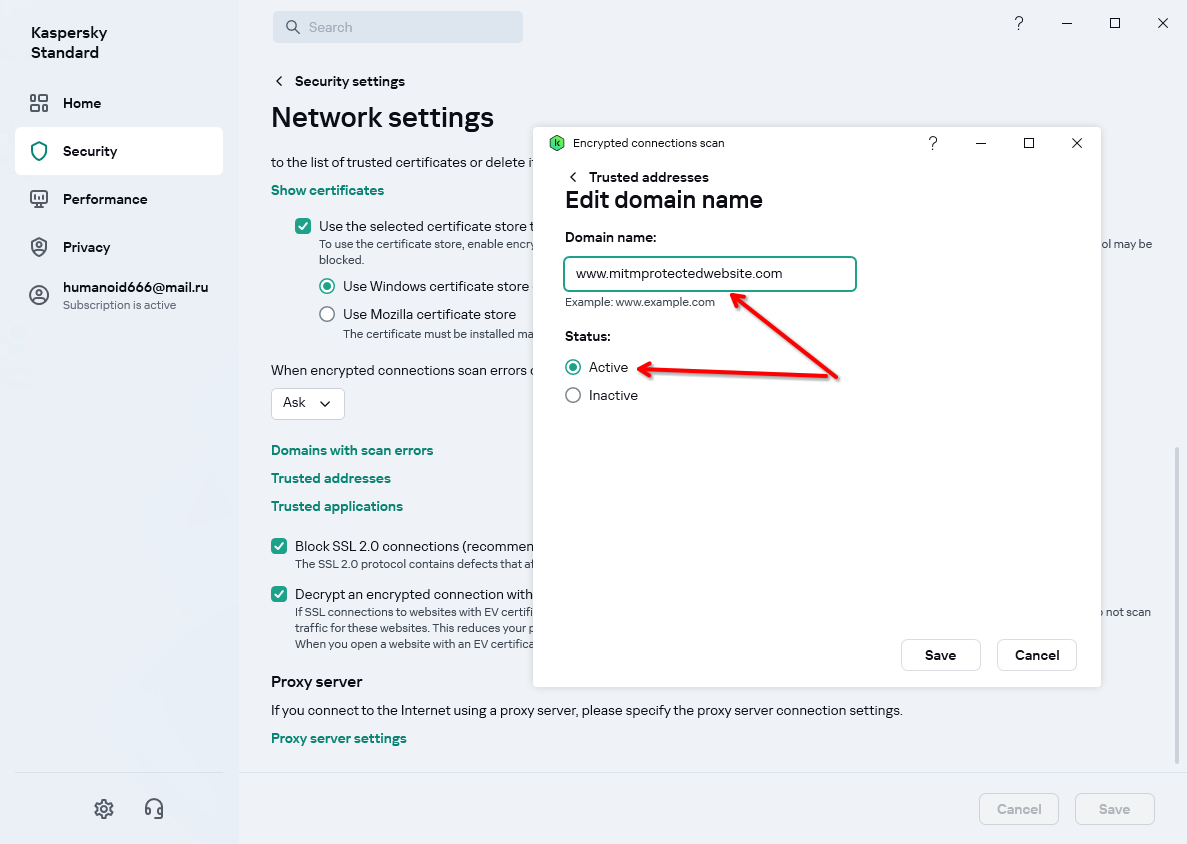
Click Trusted addresses in Encrypted connection scan section
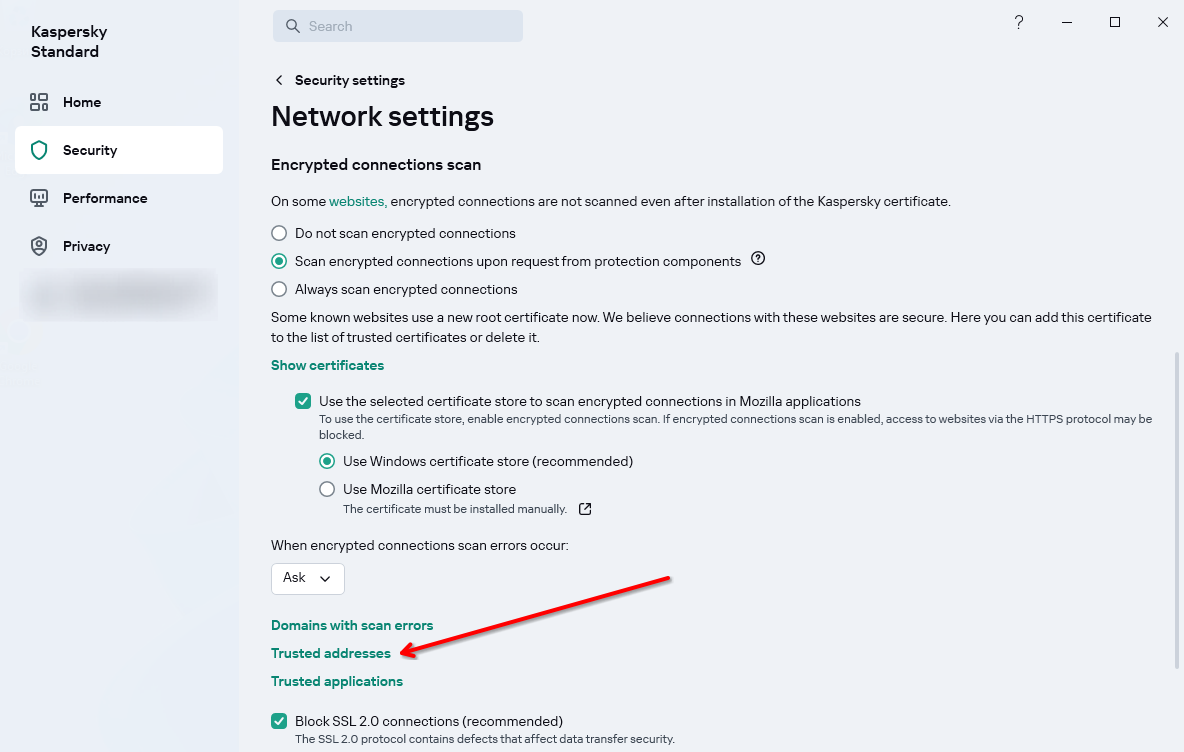
-
Enter your website URL, select Active radio button and save changes
-
Save (2) new Kaspersky settings (it will show a prompt to confirm if you really want to change settings)
-
Visit protected website again
Disable Kaspersky MITM proxy
-
Perform the steps 1-3 from the whitelisting guide above to get into MITM proxy settings
-
Choose Do not scan encrypted connections in “Encrypted Connections Scan” sections
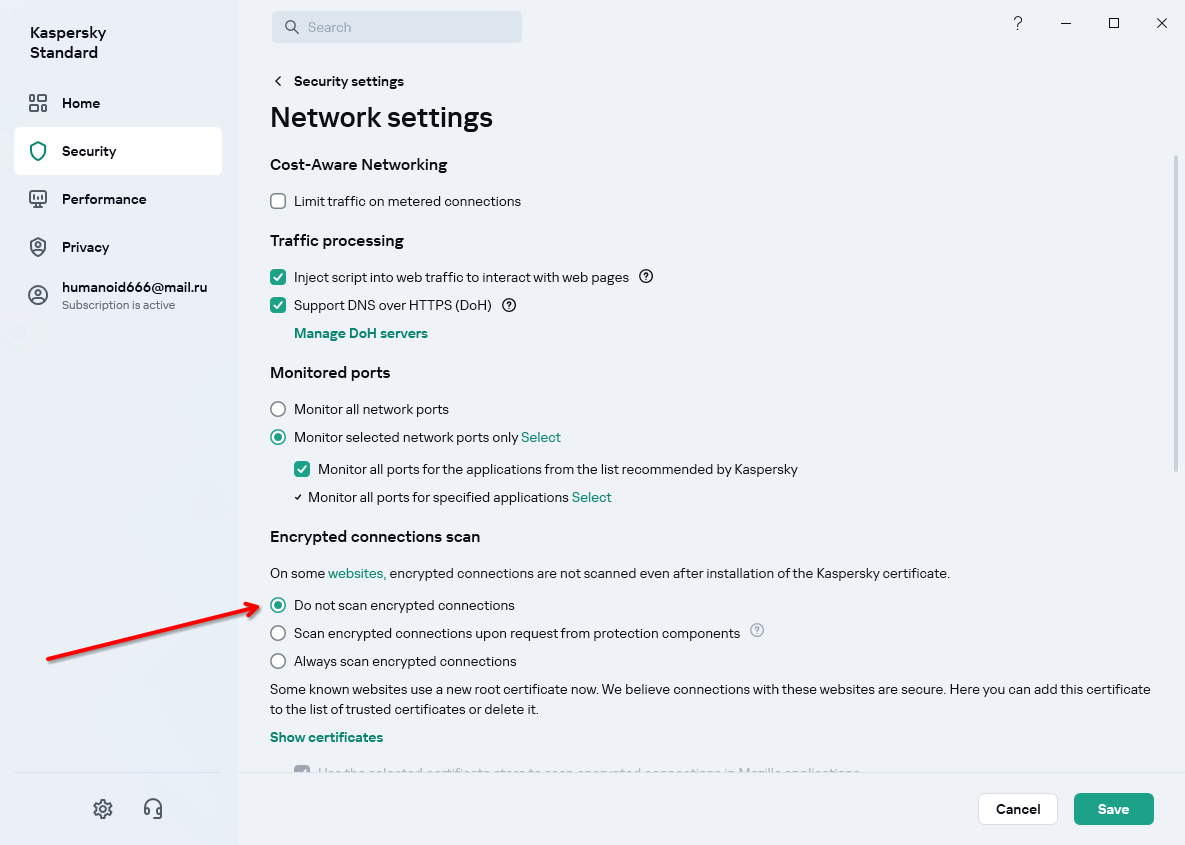
-
Read about the consequences of your decision and click Save to apply new settings
-
Visit protected website again
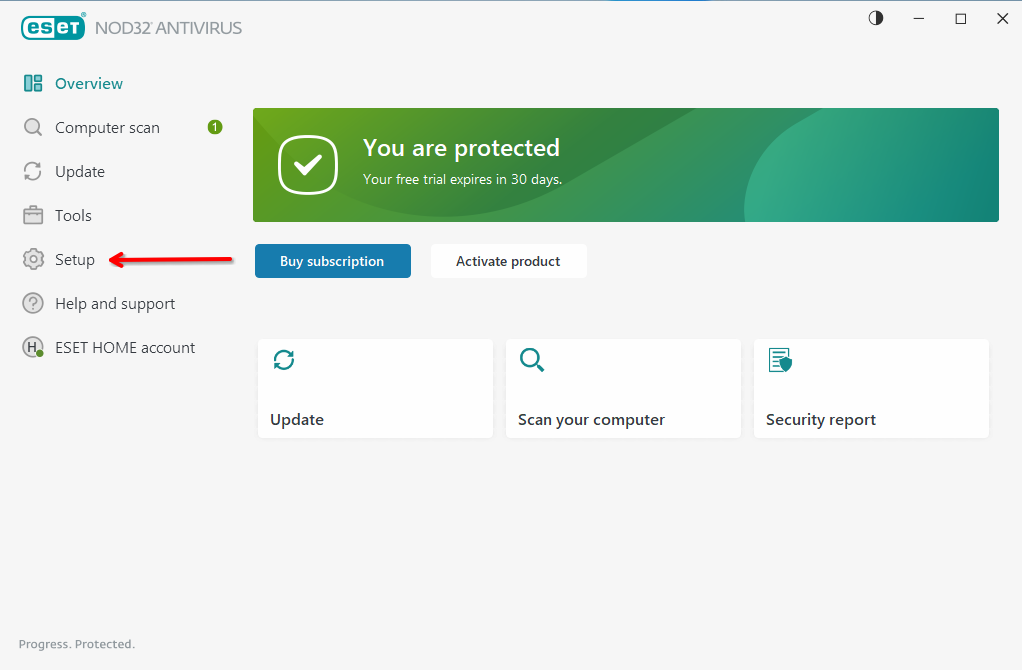
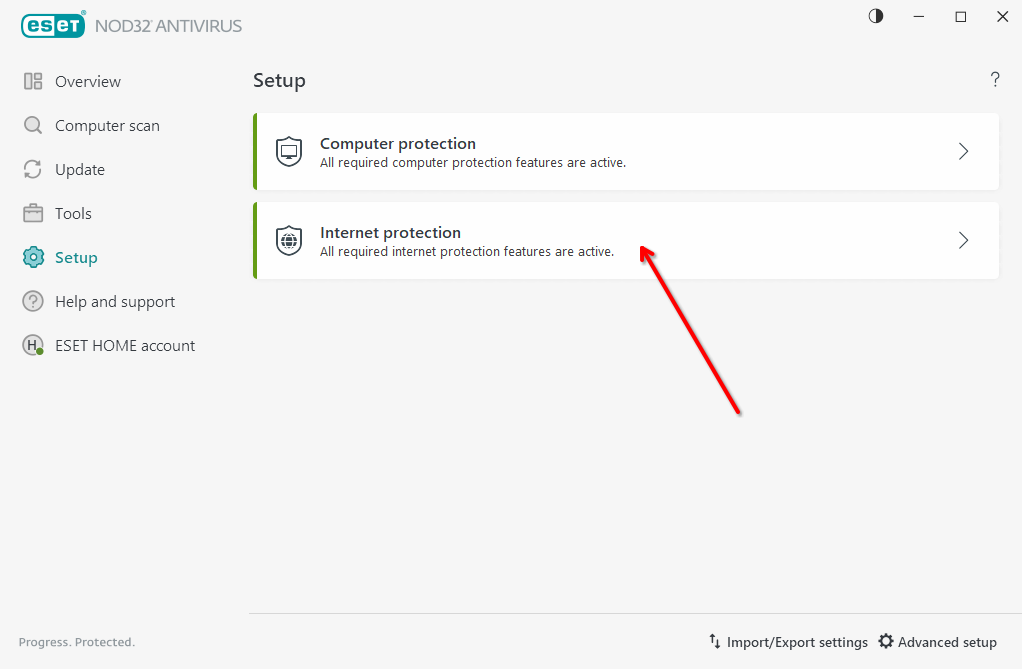
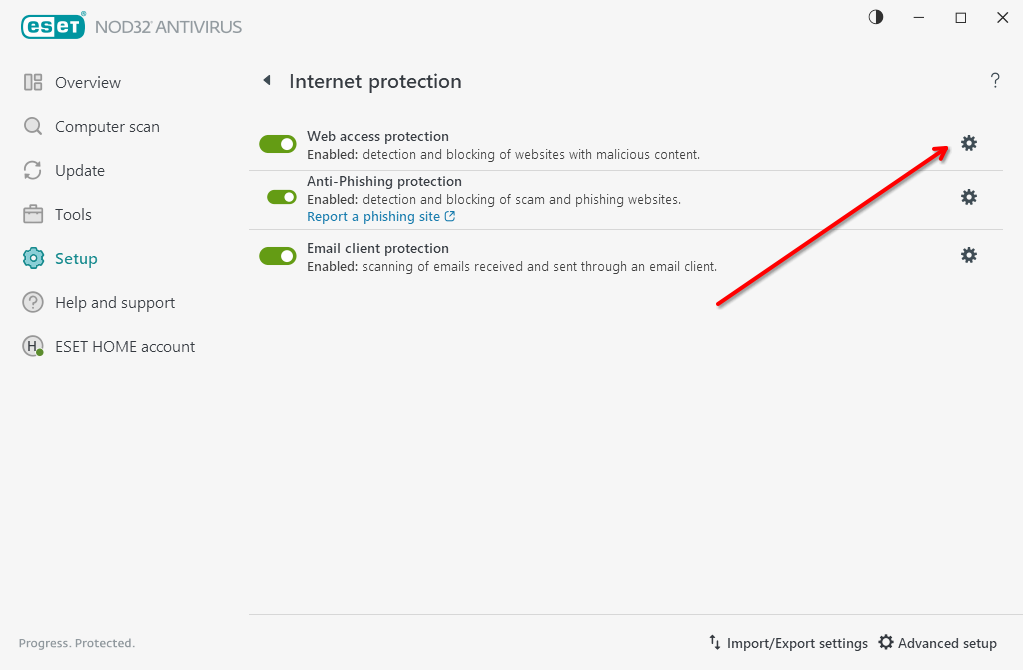
ESET NOD32
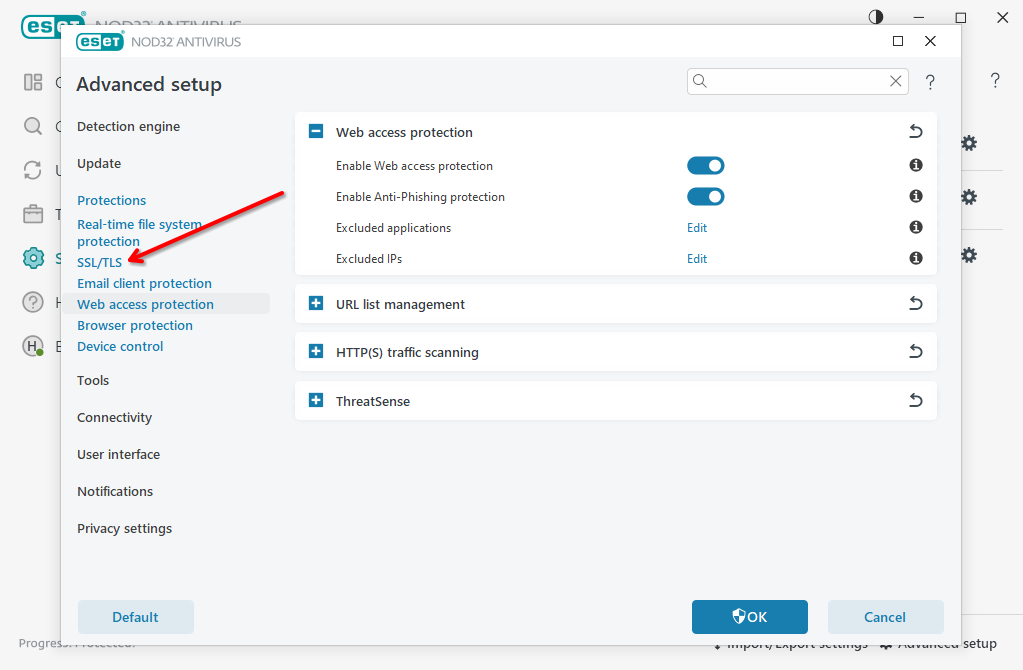
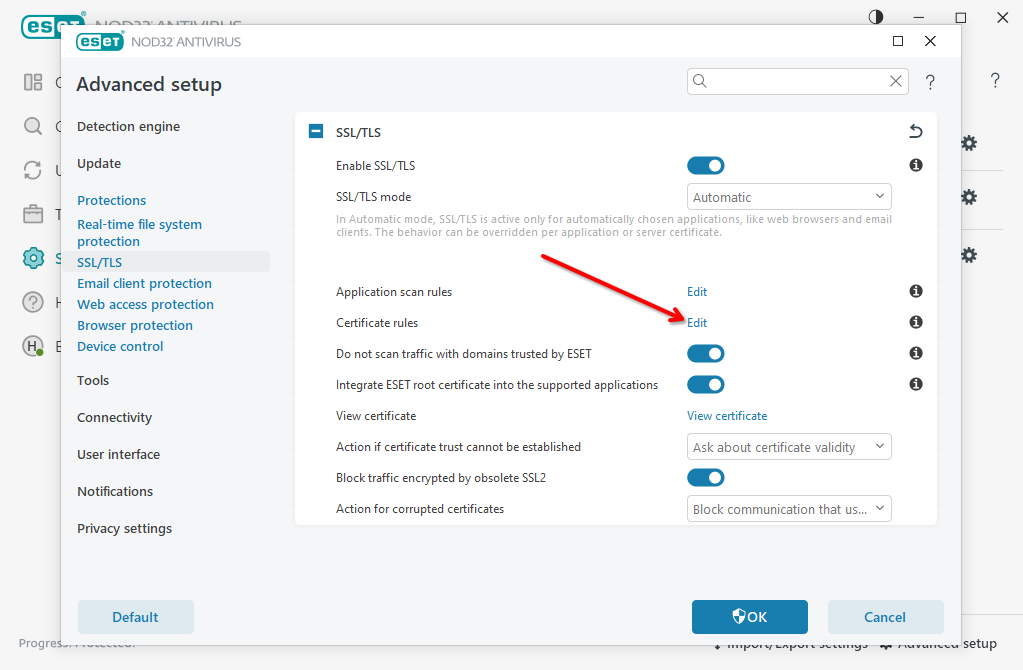
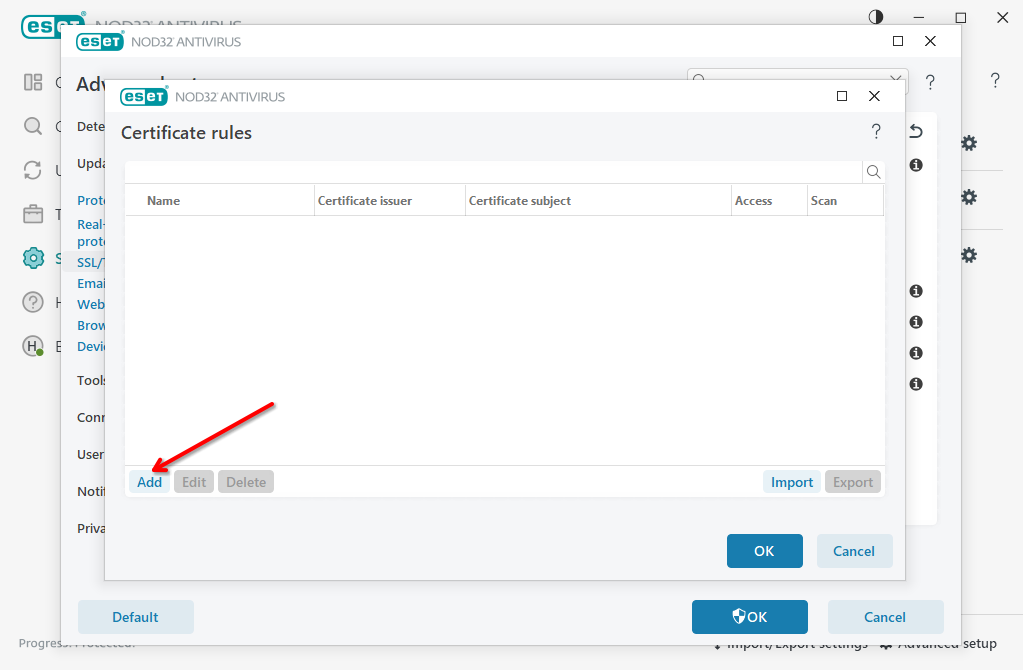
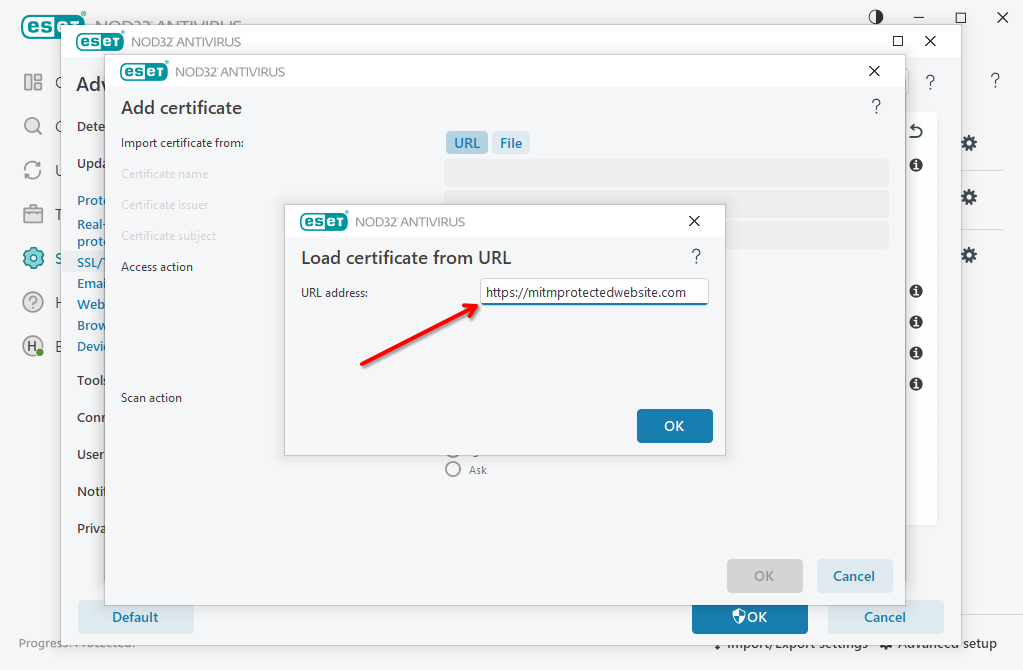
Whitelist your protected website for ESET NOD32
-
Click URL to fetch website certificate using built-in function. Alternatively, you could upload the certificate file manually
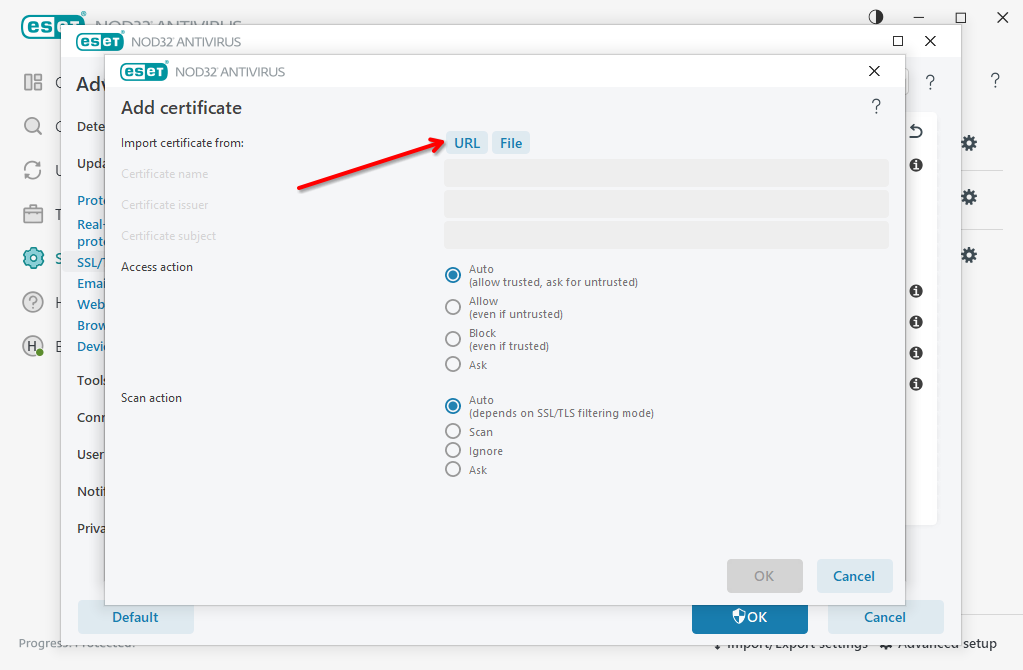
-
Set Access Action to Auto or Allow, set Scan Action to Ignore and click OK to save settings. Then click OK few more times to apply new settings.
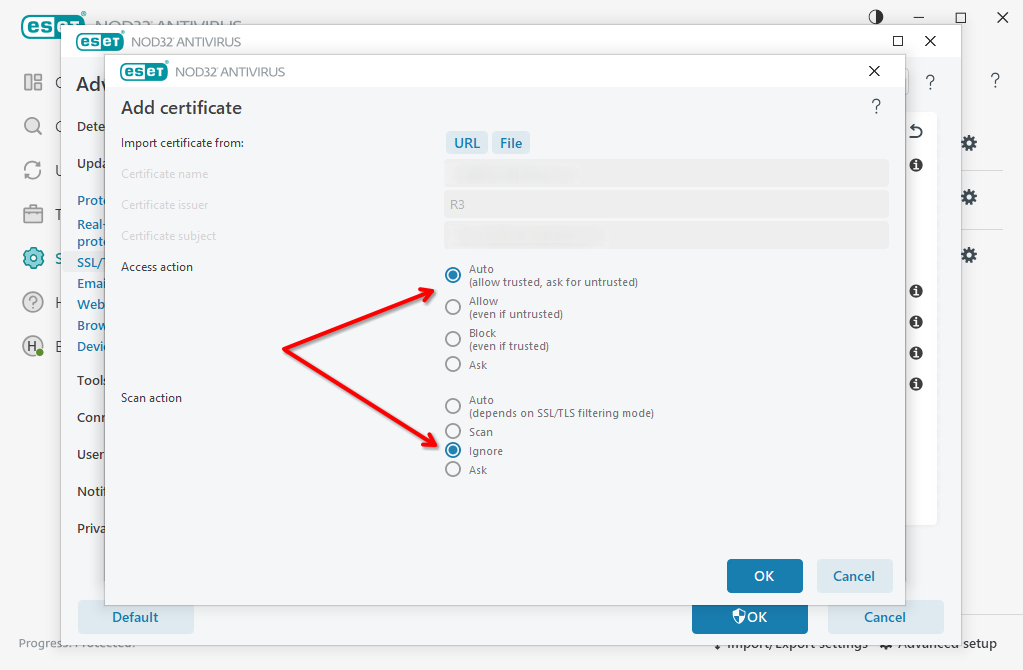
-
Visit the website again
Disable ESET NOD32 MITM proxy
-
Perform the steps 1-4 from the whitelisting guide above to get into MITM proxy settings
-
Switch off Enable SSL/TLS toggle and confirm changes pressing OK button
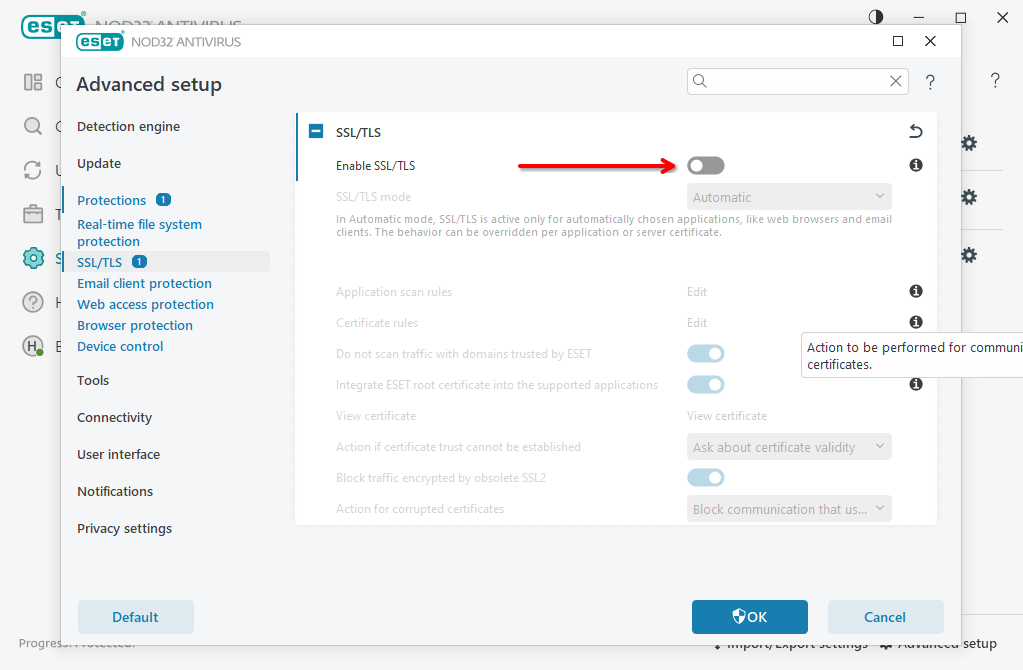
-
Visit protected website again
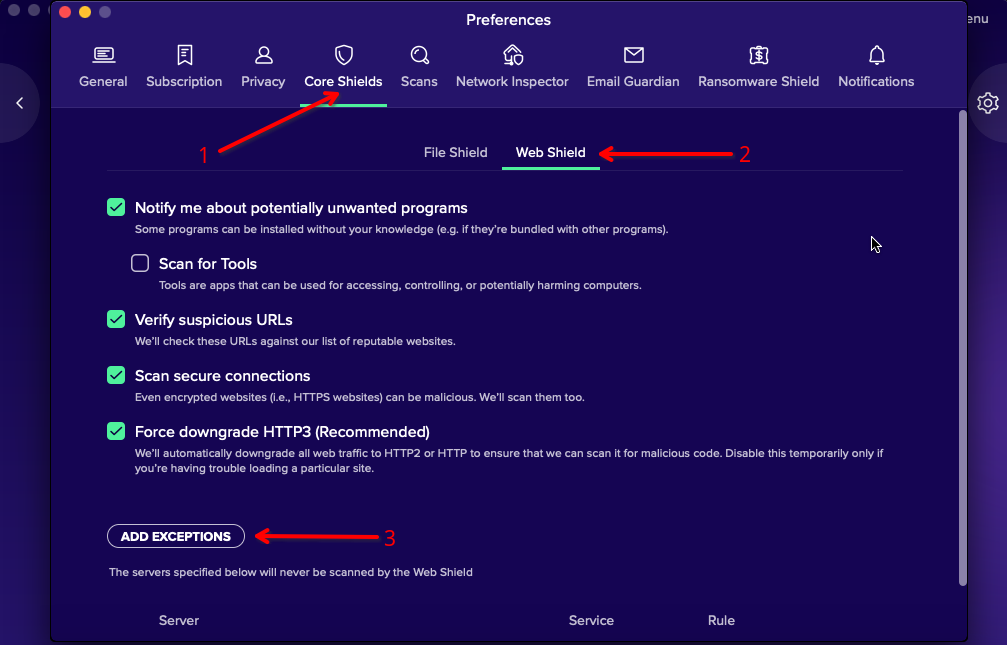
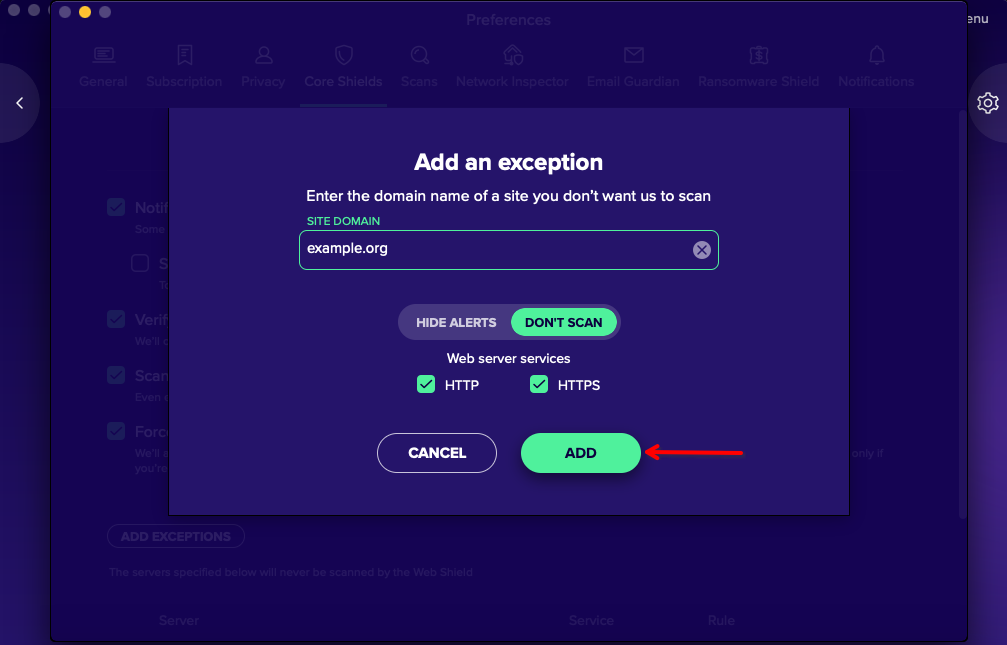
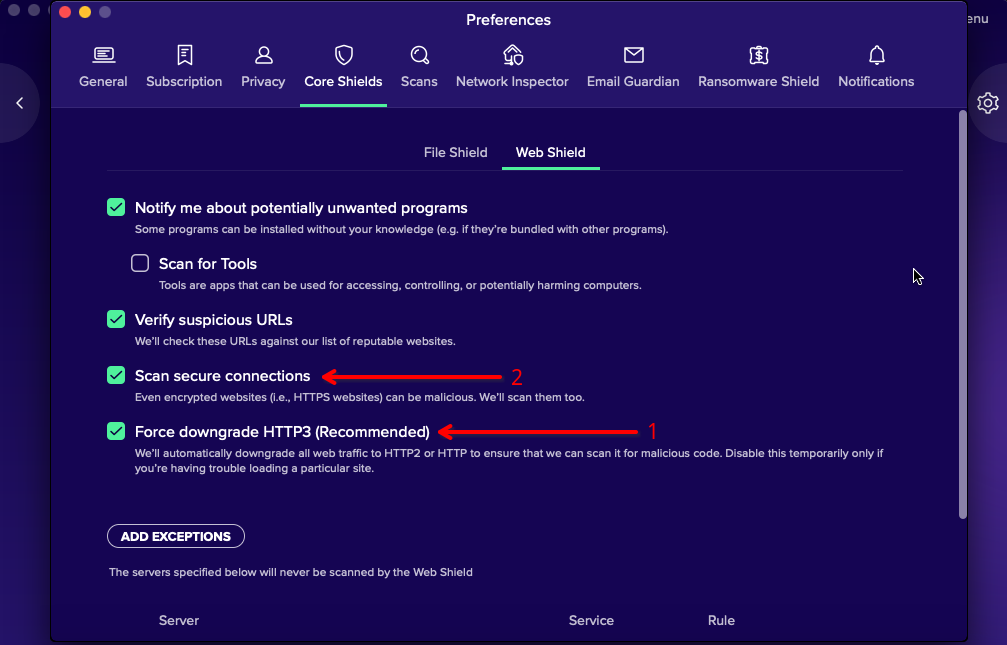
Avast (OS X)
Partner program
I would like to partner with BotGuard. Which locations are of interest to you?
We engage in many partnerships all around the world. Please contact us directly to find out more.
I would like to partner with BotGuard. Do you provide any hosting panel modules like cPanel or Plesk?
Yes, we provide modules for WHM / cPanel, Plesk and ISPmanager. Please visit Hosting panels page for more information, or contact us directly if your panel is not listed here.
Is your client dashboard available white labeled?
It is possible, but will be subject to special agreement. Please contact us directly to learn more.
How do I monitor the number of requests from my end-customers?
You will always have access to the number of visitor requests directly on your dashboard. Please keep in mind that website statistics are updated after every one thousand requests. This is done to improve system performance, so if site traffic is low, this may take some time.